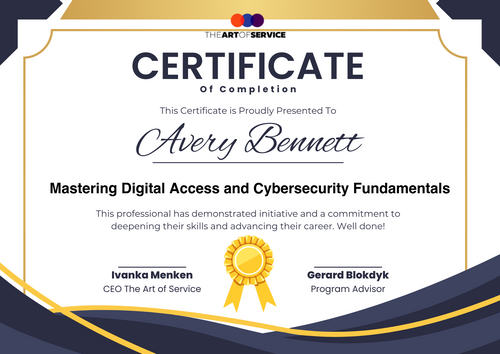
Mastering Digital Access and Cybersecurity Fundamentals
This comprehensive course is designed to equip you with the knowledge and skills necessary to master digital access and cybersecurity fundamentals. Upon completion, you will receive a certificate issued by The Art of Service.Course Features - Interactive: Engage with our expert instructors and peers through interactive discussions and activities.
- Engaging: Enjoy a user-friendly and mobile-accessible learning platform.
- Comprehensive: Cover a wide range of topics, from the basics to advanced concepts.
- Personalized: Receive personalized feedback and support from our expert instructors.
- Up-to-date: Stay current with the latest developments and advancements in digital access and cybersecurity.
- Practical: Apply theoretical concepts to real-world scenarios and projects.
- High-quality content: Learn from expert instructors with extensive experience in the field.
- Certification: Receive a certificate upon completion, issued by The Art of Service.
- Flexible learning: Access course materials at any time, from any device.
- Community-driven: Join a community of like-minded professionals and stay connected.
- Actionable insights: Gain practical knowledge and skills that can be applied immediately.
- Hands-on projects: Work on real-world projects to reinforce learning and build portfolio.
- Bite-sized lessons: Learn in manageable chunks, with each lesson building on the previous one.
- Lifetime access: Enjoy ongoing access to course materials, even after completion.
- Gamification: Engage in a fun and interactive learning experience, with rewards and recognition.
- Progress tracking: Monitor progress and stay motivated with our progress tracking feature.
Course Outline Chapter 1: Introduction to Digital Access and Cybersecurity
- 1.1 What is Digital Access?
- 1.2 What is Cybersecurity?
- 1.3 Importance of Digital Access and Cybersecurity
- 1.4 Brief History of Digital Access and Cybersecurity
- 1.5 Current Trends and Future Directions
Chapter 2: Digital Access Fundamentals
- 2.1 Types of Digital Access
- 2.2 Digital Access Technologies
- 2.3 Digital Access Protocols
- 2.4 Digital Access Security Measures
- 2.5 Best Practices for Digital Access
Chapter 3: Cybersecurity Fundamentals
- 3.1 Types of Cyber Threats
- 3.2 Cybersecurity Technologies
- 3.3 Cybersecurity Protocols
- 3.4 Cybersecurity Measures
- 3.5 Best Practices for Cybersecurity
Chapter 4: Risk Management and Compliance
- 4.1 Risk Management Fundamentals
- 4.2 Risk Assessment and Analysis
- 4.3 Risk Mitigation and Response
- 4.4 Compliance and Regulatory Requirements
- 4.5 Best Practices for Risk Management and Compliance
Chapter 5: Incident Response and Disaster Recovery
- 5.1 Incident Response Fundamentals
- 5.2 Incident Response Planning
- 5.3 Incident Response and Containment
- 5.4 Disaster Recovery Fundamentals
- 5.5 Disaster Recovery Planning and Implementation
Chapter 6: Security Awareness and Training
- 6.1 Security Awareness Fundamentals
- 6.2 Security Awareness Training
- 6.3 Security Awareness Best Practices
- 6.4 Role-Based Security Awareness Training
- 6.5 Security Awareness and Culture
Chapter 7: Digital Forensics and Incident Response
- 7.1 Digital Forensics Fundamentals
- 7.2 Digital Forensics Tools and Techniques
- 7.3 Incident Response and Digital Forensics
- 7.4 Digital Forensics Best Practices
- 7.5 Digital Forensics and Incident Response Case Studies
Chapter 8: Cloud Security and Virtualization
- 8.1 Cloud Security Fundamentals
- 8.2 Cloud Security Risks and Threats
- 8.3 Cloud Security Measures and Controls
- 8.4 Virtualization Security Fundamentals
- 8.5 Virtualization Security Risks and Threats
Chapter 9: Network Security and Architecture
- 9.1 Network Security Fundamentals
- 9.2 Network Security Risks and Threats
- 9.3 Network Security Measures and Controls
- 9.4 Network Architecture Fundamentals
- 9.5 Network Architecture and Security
Chapter 10: Cryptography and Access Control
- 10.1 Cryptography Fundamentals
- 10.2 Cryptography Techniques and Tools
- 10.3 Access Control Fundamentals
- 10.4 Access Control Models and Techniques
- 10.5 Cryptography and Access Control Best Practices
Chapter 11: Cybersecurity Governance and Management
- 11.1 Cybersecurity Governance Fundamentals
- 11.2 Cybersecurity Governance Frameworks and Standards
- 11.3 Cybersecurity Management Fundamentals
- 11.4 Cybersecurity Management Best Practices
- 11.5 Cybersecurity Governance and Management Case Studies
Chapter 12: Cybersecurity and Digital Access Project Management
- 12.1 Project Management Fundamentals
-
Chapter 1: Introduction to Digital Access and Cybersecurity
- 1.1 What is Digital Access?
- 1.2 What is Cybersecurity?
- 1.3 Importance of Digital Access and Cybersecurity
- 1.4 Brief History of Digital Access and Cybersecurity
- 1.5 Current Trends and Future Directions
Chapter 2: Digital Access Fundamentals
- 2.1 Types of Digital Access
- 2.2 Digital Access Technologies
- 2.3 Digital Access Protocols
- 2.4 Digital Access Security Measures
- 2.5 Best Practices for Digital Access
Chapter 3: Cybersecurity Fundamentals
- 3.1 Types of Cyber Threats
- 3.2 Cybersecurity Technologies
- 3.3 Cybersecurity Protocols
- 3.4 Cybersecurity Measures
- 3.5 Best Practices for Cybersecurity
Chapter 4: Risk Management and Compliance
- 4.1 Risk Management Fundamentals
- 4.2 Risk Assessment and Analysis
- 4.3 Risk Mitigation and Response
- 4.4 Compliance and Regulatory Requirements
- 4.5 Best Practices for Risk Management and Compliance
Chapter 5: Incident Response and Disaster Recovery
- 5.1 Incident Response Fundamentals
- 5.2 Incident Response Planning
- 5.3 Incident Response and Containment
- 5.4 Disaster Recovery Fundamentals
- 5.5 Disaster Recovery Planning and Implementation
Chapter 6: Security Awareness and Training
- 6.1 Security Awareness Fundamentals
- 6.2 Security Awareness Training
- 6.3 Security Awareness Best Practices
- 6.4 Role-Based Security Awareness Training
- 6.5 Security Awareness and Culture
Chapter 7: Digital Forensics and Incident Response
- 7.1 Digital Forensics Fundamentals
- 7.2 Digital Forensics Tools and Techniques
- 7.3 Incident Response and Digital Forensics
- 7.4 Digital Forensics Best Practices
- 7.5 Digital Forensics and Incident Response Case Studies
Chapter 8: Cloud Security and Virtualization
- 8.1 Cloud Security Fundamentals
- 8.2 Cloud Security Risks and Threats
- 8.3 Cloud Security Measures and Controls
- 8.4 Virtualization Security Fundamentals
- 8.5 Virtualization Security Risks and Threats
Chapter 9: Network Security and Architecture
- 9.1 Network Security Fundamentals
- 9.2 Network Security Risks and Threats
- 9.3 Network Security Measures and Controls
- 9.4 Network Architecture Fundamentals
- 9.5 Network Architecture and Security
Chapter 10: Cryptography and Access Control
- 10.1 Cryptography Fundamentals
- 10.2 Cryptography Techniques and Tools
- 10.3 Access Control Fundamentals
- 10.4 Access Control Models and Techniques
- 10.5 Cryptography and Access Control Best Practices
Chapter 11: Cybersecurity Governance and Management
- 11.1 Cybersecurity Governance Fundamentals
- 11.2 Cybersecurity Governance Frameworks and Standards
- 11.3 Cybersecurity Management Fundamentals
- 11.4 Cybersecurity Management Best Practices
- 11.5 Cybersecurity Governance and Management Case Studies
Chapter 12: Cybersecurity and Digital Access Project Management
- 12.1 Project Management Fundamentals